Reentrancy Attacks in 2026: Why They Still Happen
Reentrancy attacks remain a persistent threat in DeFi. Learn how they work, why they still happen in 2026, and how developers can prevent them.
Reentrancy Attacks in 2026: Why They Still Happen
Smart contract security has improved significantly over the years, yet certain vulnerabilities continue to appear in modern decentralized applications. Among these, reentrancy attacks remain one of the most well-known and persistent threats in the Ethereum ecosystem.
First widely recognized during the 2016 DAO exploit, reentrancy vulnerabilities occur when a smart contract allows external calls before updating its internal state. This seemingly small design mistake can allow attackers to repeatedly call a function and drain funds from a contract.
Even in 2026, reentrancy vulnerabilities still appear in DeFi protocols due to complex contract interactions, upgradeable systems, and insufficient validation during development.
Understanding Reentrancy
Reentrancy occurs when a contract sends funds or calls another contract before completing its internal logic.
If the receiving contract contains malicious code, it can call back into the vulnerable contract before the first execution finishes.
Because the contract state has not yet been updated, the attacker can repeatedly trigger the withdrawal function, allowing them to extract funds multiple times.
This creates a loop where the contract continues sending funds until its balance is depleted.
How Reentrancy Attacks Work
In a typical scenario, the vulnerable contract performs the following sequence:
- The user requests a withdrawal.
- The contract sends funds to the user's address.
- The contract updates the user's balance.
The issue occurs when step 2 happens before step 3.
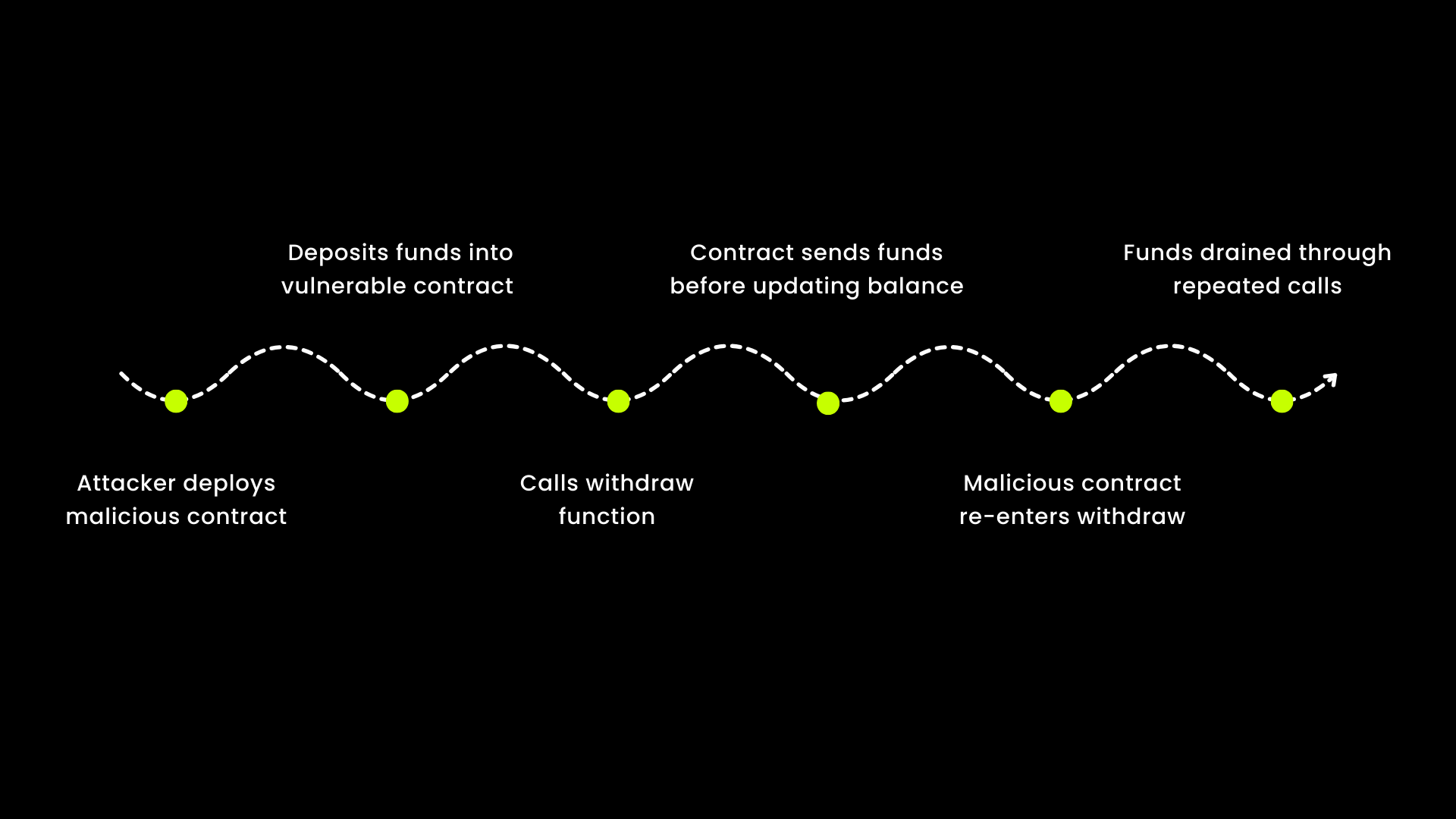
If the receiving address is a malicious contract, it can immediately call the withdrawal function again before the balance update occurs.
This allows the attacker to withdraw funds repeatedly.
Why Reentrancy Still Appears in Modern DeFi
Although the vulnerability is widely known, several factors contribute to its continued presence in smart contracts.
- Complex contract interactions:Modern DeFi systems often involve multiple contracts interacting with each other, increasing the chance of unsafe external calls.
- Upgradeable contract architectures:Upgrade mechanisms may introduce new logic that accidentally reintroduces reentrancy risks.
- Insufficient testing of edge cases:Some vulnerabilities only appear during unusual transaction sequences that standard testing may not capture.
Preventing Reentrancy Vulnerabilities
Developers can significantly reduce reentrancy risks by following several best practices.
- Use the Checks-Effects-Interactions pattern:Update contract state before performing external calls.
- Implement reentrancy guards:Libraries such as OpenZeppelin's ReentrancyGuard prevent multiple function executions within the same transaction.
- Limit external calls:Avoid unnecessary contract interactions when transferring assets.
- Conduct thorough audits:Security audits help identify unsafe call sequences and potential vulnerabilities.
Final Thoughts
Reentrancy attacks are a reminder that even well-understood vulnerabilities can persist if secure coding practices are not consistently applied.
As DeFi protocols become more complex, developers must prioritize secure contract architecture and thorough testing to prevent similar exploits.
While tools and frameworks continue to evolve, the most effective defense remains careful design and security-focused development practices.
Don't launch vulnerable code. Our team will review your smart contracts and deliver a full audit report within 48 hours.
Related Posts
Tags
Get Audited
Protect your protocol before attackers do. Request a full smart contract audit from 0xTeam.
Request Audit