Solv Protocol Exploit: How a Minting Flaw Cost $2.7 Million
A seemingly minor vulnerability in token minting logic cost the Solv Protocol $2.7 million. Explore how the exploit unfolded and the security lessons learned.
Solv Protocol Exploit: How a Minting Flaw Cost $2.7 Million
Decentralized finance protocols are often designed with strong economic incentives and complex smart contract architectures.However, even well-designed systems can fail when a small logic flaw slips through the development process.
The recent Solv Protocol exploit is a clear example of how a seemingly minor vulnerability in token minting logic can escalate into a multi-million-dollar loss.
In early March 2026, an attacker exploited a vulnerability in a BRO vault contract within Solv’s ecosystem.By abusing a minting flaw, the attacker managed to generate an inflated amount of tokens and ultimately extract approximately $2.7 million worth of assets.
While the exploit was contained quickly and affected a limited number of users, it highlights an important lesson for DeFi protocols: token minting mechanisms must be designed with extreme caution.
Understanding Solv Protocol
Solv Protocol focuses on creating financial infrastructure for Bitcoin-related DeFi products.One of its core mechanisms involves structured vaults and tokenized financial instruments that allow users to participate in yield strategies.
Within this framework, vault contracts manage the issuance and redemption of protocol tokens.
The system typically operates through the following process:
- Users deposit assets into a vault contract
- The protocol issues corresponding tokens representing the deposit
- These tokens can be used within DeFi strategies
- When users withdraw, the protocol burns the tokens and releases the underlying assets
This process relies heavily on accurate minting and burning logic.If the minting process can be manipulated, attackers may be able to generate tokens without depositing equivalent value.
What Happened During the Exploit
The Solv exploit originated from a logic flaw in the vault minting mechanism.
Under normal conditions, the vault contract verifies deposits before issuing tokens.However, the attacker discovered a way to trigger the minting function multiple times under conditions where the validation checks did not fully prevent repeated execution.
By exploiting this flaw, the attacker was able to mint BRO tokens repeatedly without depositing equivalent collateral.
Once the attacker had accumulated a large amount of these tokens, they converted them into SolvBTC, effectively extracting real value from the protocol.
The exploit was executed rapidly, allowing the attacker to drain approximately 38 SolvBTC, valued at around $2.7 million at the time of the incident.
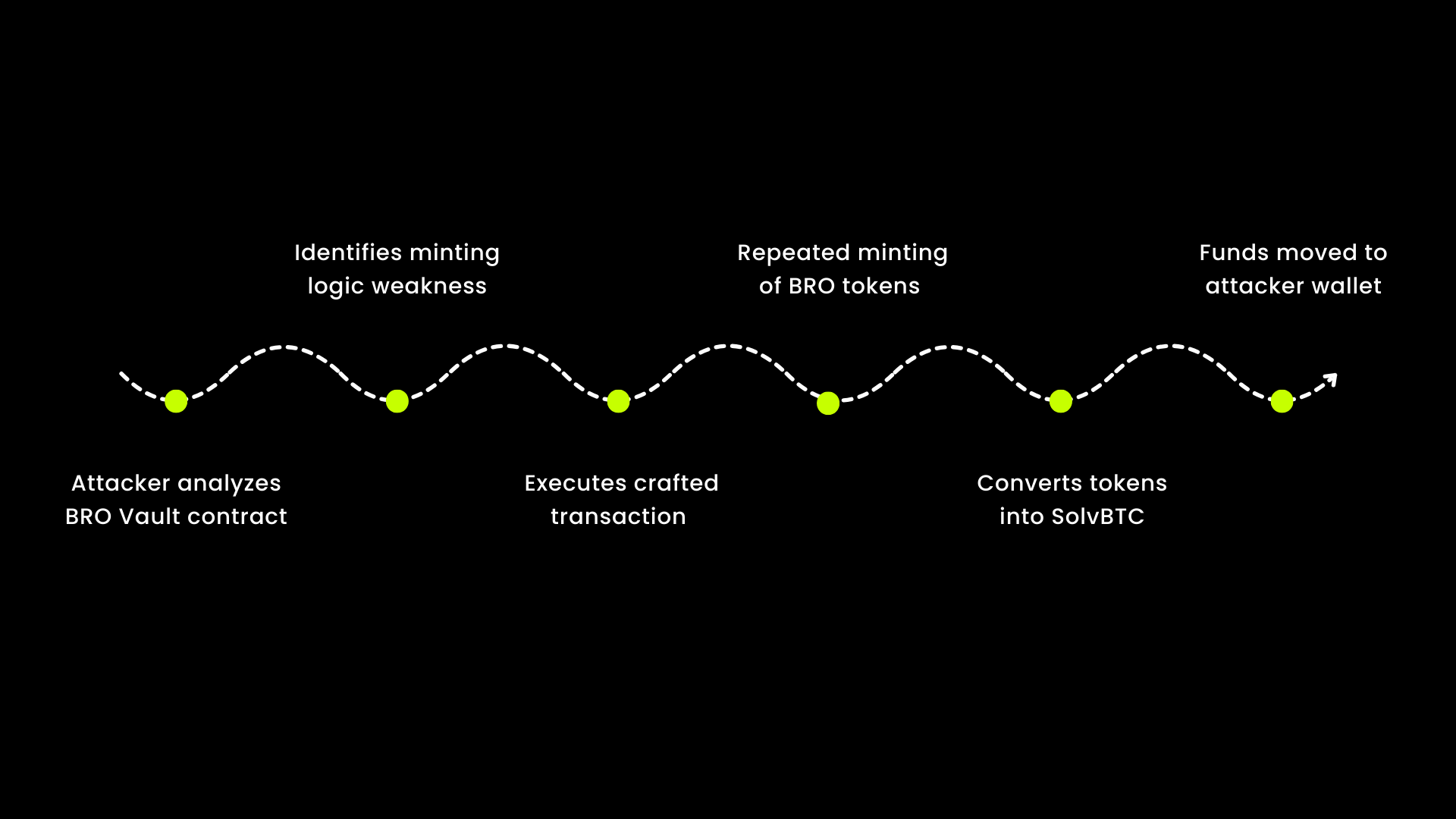
Attack Flow
Below is a simplified breakdown of how the exploit likely unfolded.
- Step 1 — Attacker Identifies Vault Logic Flaw:The attacker analyzed the BRO vault smart contract and discovered that the minting logic could be triggered in a way that allowed multiple mint operations from a single valid condition.
- Step 2 — Initial Interaction With Vault Contract:The attacker interacted with the vault contract, initiating the minting process through a crafted transaction.
- Step 3 — Repeated Token Minting:Because of the validation flaw, the attacker was able to call the minting mechanism multiple times, generating an inflated supply of BRO tokens.
- Step 4 — Token Supply Inflation:The attacker accumulated a significant amount of BRO tokens that were not backed by real deposits.
- Step 5 — Conversion to SolvBTC:The attacker swapped or redeemed these tokens into SolvBTC, turning the artificially minted tokens into valuable assets.
- Step 6 — Funds Moved to External Wallets:Finally, the attacker transferred the extracted assets to external addresses, completing the exploit.
Why This Vulnerability Was Dangerous
Minting logic vulnerabilities are particularly severe in DeFi because they directly affect token supply integrity.
If attackers can generate tokens without corresponding deposits, they effectively create unbacked assets that can be exchanged for real liquidity.
This can quickly drain vaults or liquidity pools, especially when automated market mechanisms treat the tokens as legitimate assets.
In many cases, these exploits are executed within minutes because once attackers confirm the vulnerability, they attempt to extract as much value as possible before the protocol can react.
Security Lessons for DeFi Developers
The Solv exploit reinforces several important security principles for smart contract development.
- Strict Minting Validation:Mint functions must ensure that token issuance is always tied to verifiable collateral deposits. Any edge cases that allow repeated execution must be eliminated.
- Comprehensive Contract Testing:Unit tests and fuzz testing should specifically focus on scenarios involving token minting and redemption.
- Rate Limits and Circuit Breakers:Protocols can implement safeguards that temporarily halt minting if abnormal supply increases are detected.
- Continuous Monitoring:Real-time monitoring systems can detect unusual minting activity and allow teams to pause contracts before large losses occur.
Final Thoughts
The Solv Protocol exploit highlights how small logic flaws in financial smart contracts can have significant consequences.
While DeFi innovation continues to accelerate, security must remain a top priority throughout the development lifecycle.
Protocols that invest in rigorous testing, comprehensive audits, and continuous monitoring are far better positioned to protect user funds and maintain trust within the ecosystem.
As the industry grows, incidents like this will continue to shape how developers design safer and more resilient financial infrastructure on-chain.
Don't launch vulnerable code. Our team will review your smart contracts and deliver a full audit report within 48 hours.
Related Posts
Tags
Get Audited
Protect your protocol before attackers do. Request a full smart contract audit from 0xTeam.
Request Audit